October/2022 Latest Braindump2go NSE5_EDR-5.0 Exam Dumps with PDF and VCE Free Updated Today! Following are some new Braindump2go NSE5_EDR-5.0 Real Exam Questions!
Question: 1
What is the purpose of the Threat Hunting feature?
A. Delete any file from any collector in the organization
B. Find and delete all instances of a known malicious file or hash in the organization
C. Identify all instances of a known malicious file or hash and notify affected users
D. Execute playbooks to isolate affected collectors in the organization
Answer: C
Question: 2
How does FortiEDR implement post-infection protection?
A. By preventing data exfiltration or encryption even after a breach occurs
B. By using methods used by traditional EDR
C. By insurance against ransomware
D. By real-time filtering to prevent malware from executing
Answer: D
Question: 3
Exhibit.

Based on the forensics data shown in the exhibit which two statements are true? (Choose two.)
A. The device cannot be remediated
B. The event was blocked because the certificate is unsigned
C. Device C8092231196 has been isolated
D. The execution prevention policy has blocked this event.
Answer: B, C
Question: 4
What is the benefit of using file hash along with the file name in a threat hunting repository search?
A. It helps to make sure the hash is really a malware
B. It helps to check the malware even if the malware variant uses a different file name
C. It helps to find if some instances of the hash are actually associated with a different file
D. It helps locate a file as threat hunting only allows hash search
Answer: C
Question: 5
Exhibit.

Based on the event shown in the exhibit which two statements about the event are true? (Choose two.)
A. The device is moved to isolation.
B. Playbooks is configured for this event.
C. The event has been blocked
D. The policy is in simulation mode
Answer: B, D
Question: 6
An administrator needs to restrict access to the ADMINISTRATION tab in the central manager for a specific account.
What role should the administrator assign to this account?
A. Admin
B. User
C. Local Admin
D. REST API
Answer: C
Question: 7
Refer to the exhibit.
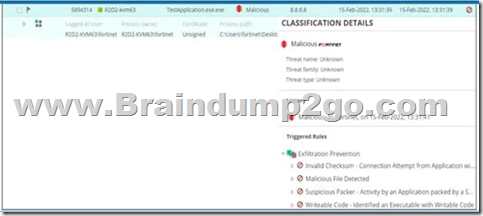
Based on the event shown in the exhibit, which two statements about the event are true? (Choose two.)
A. The NGAV policy has blocked TestApplication exe
B. TestApplication exe is sophisticated malware
C. The user was able to launch TestApplication exe
D. FCS classified the event as malicious
Answer: A, B
Question: 8
Refer to the exhibits.
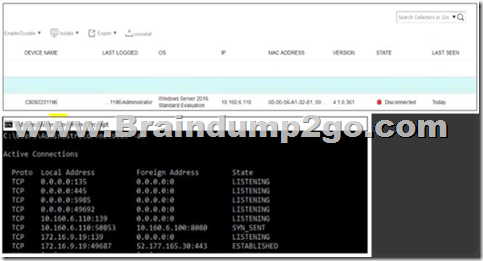
The exhibits show the collector state and active connections. The collector is unable to connect to aggregator IP address 10.160.6.100 using default port.
Based on the netstat command output what must you do to resolve the connectivity issue?
A. Reinstall collector agent and use port 443
B. Reinstall collector agent and use port 8081
C. Reinstall collector agent and use port 555
D. Reinstall collector agent and use port 6514
Answer: B
Question: 9
Refer to the exhibits.
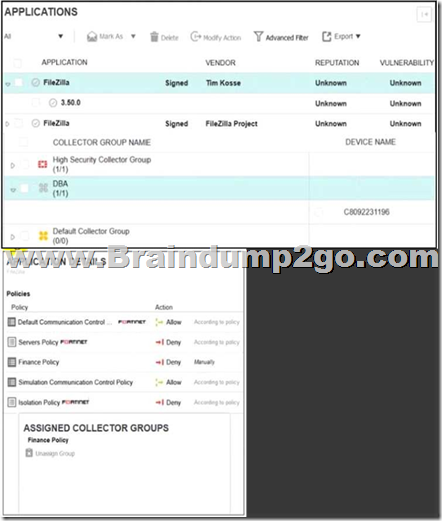
The exhibits show application policy logs and application details Collector C8092231196 is a member of the Finance group
What must an administrator do to block the FileZilia application?
A. Deny application in Finance policy
B. Assign Finance policy to DBA group
C. Assign Finance policy to Default Collector Group
D. Assign Simulation Communication Control Policy to DBA group
Answer: D
Question: 10
Refer to the exhibit.
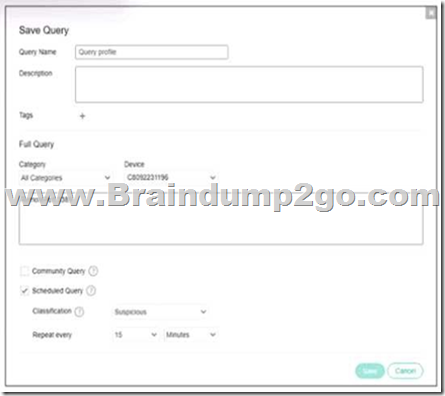
Based on the threat hunting query shown in the exhibit which of the following is true?
A. RDP connections will be blocked and classified as suspicious
B. A security event will be triggered when the device attempts a RDP connection
C. This query is included in other organizations
D. The query will only check for network category
Answer: B
Question: 11
Which connectors can you use for the FortiEDR automated incident response? (Choose two.)
A. FortiNAC
B. FortiGate
C. FortiSiem
D. FortiSandbox
Answer: B, C
Question: 12
What is true about classifications assigned by Fortinet Cloud Sen/ice (FCS)?
A. The core is responsible for all classifications if FCS playbooks are disabled
B. The core only assigns a classification if FCS is not available
C. FCS revises the classification of the core based on its database
D. FCS is responsible for all classifications
Answer: C
Question: 13
Refer to the exhibit.
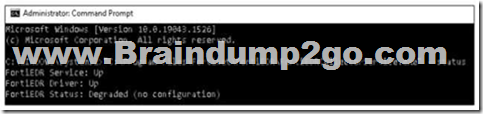
Based on the FortiEDR status output shown in the exhibit, which two statements about the FortiEDR collector are true? (Choose two.)
A. The collector device has windows firewall enabled
B. The collector has been installed with an incorrect port number
C. The collector has been installed with an incorrect registration password
D. The collector device cannot reach the central manager
Answer: B, D
Question: 14
A company requires a global communication policy for a FortiEDR multi-tenant environment. How can the administrator achieve this?
A. An administrator creates a new communication control policy and shares it with other organizations
B. A local administrator creates new a communication control policy and shares it with other organizations
C. A local administrator creates a new communication control policy and assigns it globally to all organizations
D. An administrator creates a new communication control policy for each organization
Answer: C
Question: 15
Refer to the exhibit.
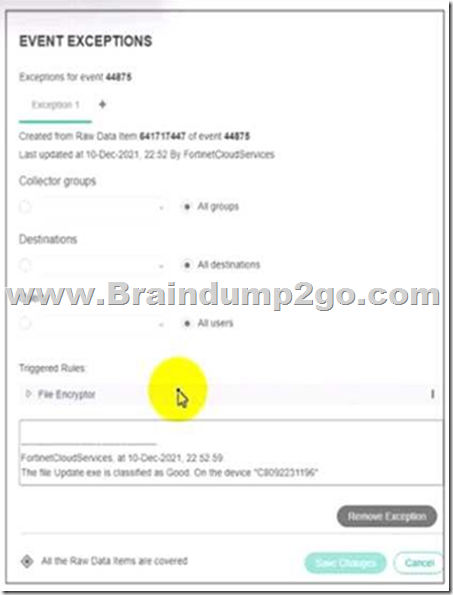
Based on the event exception shown in the exhibit which two statements about the exception are true? (Choose two)
A. A partial exception is applied to this event
B. FCS playbooks is enabled by Fortinet support
C. The exception is applied only on device C8092231196
D. The system owner can modify the trigger rules parameters
Answer: A, C
Question: 16
Which two statements are true about the remediation function in the threat hunting module? (Choose two.)
A. The file is removed from the affected collectors
B. The threat hunting module sends the user a notification to delete the file
C. The file is quarantined
D. The threat hunting module deletes files from collectors that are currently online.
Answer: B, C
Question: 17
Exhibit.

Based on the forensics data shown in the exhibit, which two statements are true? (Choose two.)
A. An exception has been created for this event
B. The forensics data is displayed m the stacks view
C. The device has been isolated
D. The exfiltration prevention policy has blocked this event
Answer: C, D
Question: 18
The FortiEDR axe classified an event as inconclusive, out a few seconds later FCS revised the classification to malicious. What playbook actions ate applied to the event?
A. Playbook actions applied to inconclusive events
B. Playbook actions applied to handled events
C. Playbook actions applied to suspicious events
D. Playbook actions applied to malicious events
Answer: D
Question: 19
Which threat hunting profile is the most resource intensive?
A. Comprehensive
B. Inventory
C. Default
D. Standard Collection
Answer: A
Question: 20
Which two types of remote authentication does the FortiEDR management console support? (Choose two.)
A. Radius
B. SAML
C. TACACS
D. LDAP
Answer: A, D
Resources From:
1.2022 Latest Braindump2go NSE5_EDR-5.0 Exam Dumps (PDF & VCE) Free Share:
https://www.braindump2go.com/nse5-edr-5-0.html
2.2022 Latest Braindump2go NSE5_EDR-5.0 PDF and NSE5_EDR-5.0 VCE Dumps Free Share:
https://drive.google.com/drive/folders/1CJgO_BfQSuot7WsvGWbiEpNGJwTDPrDd?usp=sharing
3.2021 Free Braindump2go NSE5_EDR-5.0 Exam Questions Download:
https://www.braindump2go.com/free-online-pdf/NSE5_EDR-5.0-PDF-Dumps(1-20).pdf
Free Resources from Braindump2go,We Devoted to Helping You 100% Pass All Exams!